June 4th, 2009
Day Three recap from Wendy M. Grossman.
“Do you feel guilty about killing newspapers?” Saul Hansell asked Craig Newmark yesterday. The founder of Craig’s List, widely credited with stealing newspapers’ classified ads, offered the mildly presented answer that it would be more correct to say that Craig’s List, Amazon, and eBay took the newspapers’ audience by offering them a more friendly and convenient marketplace.
At some point in the early 19-00s, Charlotte-Anne Lucas explained today, newspapers changed from charging for content to charging for audiences, leading them to selecting content based on its mass appeal. Exactly, she didn’t say, like AOL in the mid 1990s, when it switched from making its money from connect time, which favored all sorts of niche content, to making its money from advertising, which required mass eyeballs.
More>
Posted in Uncategorized | Comments Off
June 4th, 2009
Mark Belinsky, co-director of the nonprofit Digital Democracy, and a guest blogger for the conference writes from the cloud on the second part of the second day of the conference.
He covers privacy, censorship and circumvention as well as laws on cloud computing and some research. READ MORE!

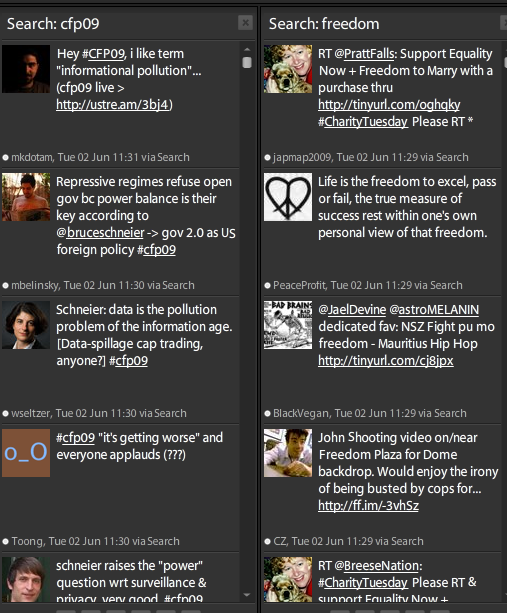
Word Cloud of Popular Words at CFP09
Tags: censorship, cfp09, future, privacy, security
Posted in Uncategorized | Comments Off
June 4th, 2009
Jim Harper writes on CATO@LIBERTY about internet censorship in China:
Today marks the 20th anniversary of the massacre of students and other anti-authoritarian protests in Tiananmen square.
If you want background info, including causes and the wider political context, check Wikipedia.
You can also see stirring videos on Youtube.
There are incredible photos on Flickr.
And of course Twitter has a wealth of real-time information and thinking about the anniversary. Just search using the hash tag #Tiananmen.
But for those 1.5 billion people trapped behind the Great Firewall of China, absolutely none of those links are accessible. To mark the event that the government assures never happened, the Chinese government has blocked most social networking sites.
More>
Tags: censorship, China, Jim Harper
Posted in Uncategorized | 2 Comments »
June 4th, 2009
This morning I attended a panel discussion on The Internet and Social Change in China, moderated by Rebecca MacKinnon. Her opening address and the discussion that followed were impressive. I particularly liked that MacKinnon opened with a powerpoint featuring work from Chinese bloggers. It was great to see the ingenuity of Chinese bloggers firsthand! One video showed a group of alpacas frolicking in a field singing a children’s song in Chinese. MacKinnon explained that the lyrics, “cao ni ma”, mean “grass mud horse”. That’s what alpacas are called in Chinese. But change the tones of the words slightly (as the singers did in the video) and they means something very different…about your mother. What a crafty, funny way to protest against internet censorship in China, where the “Great Firewall” blocks content that could weaken the legitimacy of the government. Content relating to Tiananmen Square and other sensitive topics is routinely blocked, but resourceful internet users find ways to get around the censorship. In China, MacKinnon told us, the most popular search midday June 4th was “What day is June fourth?”, evading the censor that blocks “Tiananmen Square” on certain search engines. Search for “Tiananmen Square” on baidu, a Chinese search engine, and you will not get any results.
However, my lasting impression from the discussion is that the role of the internet in China is more complex than monolithic censorship of liberals. China has the largest population of internet users in the world, and the government has effectively used the internet to connect with the people. Prime Minister Wen Jiabao recently participated in a two and a half hour live chat with “netizens”, discussing policy and his private life. The “E-Congress” website has a large posting section that even featured a discussion about China’s one child policy; a discussion that was not removed from the website. Internet users also use the internet to connect with the government. Popular support organized via the internet may help a young woman named Den Yujiao, who was arrested after stabbing an official who tried to rape her. She has become a popular heroine in China, and MacKinnon believes the charges will soon be reduced if not dropped. Nationalists also use the internet in creative ways to support government policies such as the recent crackdown in Tibet.
The three panelists, Shen Tong, Hu Yong and Michael Anti, discussed how the internet has changed China on an individual and nationwide level. They all agreed that the internet is a liberalizing agent in China. Hu Yong claimed that “netizens share different values than older people” and as many as 80% have been liberalized by their exposure to the internet. Freedom of speech and democracy are more valued among netizens. Shen Tong agreed that the internet is gradually liberalizing China, but argued that immediate freedom of speech would lead to greater civil liberties and make China a “better country faster”.
Throughout the panel discussion, all four of the speakers were regularly checking their cellphones. MacKinnon assured the audience that it was not because they were bored. Instead, they were checking Twitter updates about a Tiananmen anniversary rally in Hong Kong that attracted 150,000 people.
Tags: China, conference
Posted in Uncategorized | Comments Off
June 4th, 2009
Susan Crawford of the Obama administration, kicked off CFP presentations Tuesday morning with a striking anecdote. A recent article in the Wall Street Journal quoted 37-year-old homeless man Charles Pitts:
“You don’t need a TV. You don’t need a radio. You don’t even need a newspaper. But you need the Internet.”
- On the Street and On Facebook: The Homeless Stay Wired by Phred Dvorak
It begs the question of all of us … what do you need?
An Internet connection?
A mobile phone?
An encrypted email service?
(cross-posted from guest-blogger Emily Jacobi’s blog Glean & Gleam)
Tags: conference
Posted in Uncategorized | Comments Off
June 4th, 2009
More blog and news coverage of CFP2009. If you’re blogging at CFP let us know in the comments so we can include you in our link lists!
Filtering v3.0, Derek Bambauer, INFO/LAW, 6-3-09
Securing New Infrastructure Will Require Watchful Eye, Experts Say, Douglas Streeks, Benton Foundation, 6-3-09
Computers, Freedom, and Privacy 2009 – Day Two, Wendy Grossman, net.wars via newswireless.net, 6-3-09
Online Behavioral Targeting Targeted by Feds, Critics, Ryan Singel, Wired.com’s Episcenter, 6-3-09
Obama’s Cybersecurity Plan: Bring in the Contractors!, Tom Burghardt, Pacific Free Press, 6-3-09
Google and Microsoft Defend Practices at Computers, Freedom and Privacy Conference, Ryan Womack, BroadbandCensus.com, 6-3-09
Privacy conference panel: Consumers give up privacy too easily, Donna Tapellini, ConsumerReports.org, 6-3-09
Privacy a Stumbling Block in Healthcare IT, Kenneth Corbin, internetnews.com, 6-3-09
CFP 2009 Part 1: Threats to Privacy, Jeff Porten, TidBITS: Mac News for the Rest of Us, 6-3-09
Behavioral Targeting To Rescue Newspapers?, Wendy Davis, The Daily Online Examiner, 6-3-09
Tracking and collecting online data, p2pnet news, 6-3-09
Pot shots at the Google Book Search deal, Kenneth Corbin, internetnews.com, 6-2-09
Tags: CFP&N
Posted in Uncategorized | 1 Comment »
June 3rd, 2009
Gust blogger Mark Belinsky has another blog post available covering the first half of Day 2.
He covers the opening ceremonies and reactions to information that China blocked access to Twitter, Hotmail, Windows Live, Bing, Flickr, YouTube, The Huffington Post, Blogspot, and some other sites in advance of the Tienanmen Square Anniversary. And the thread of open government that was woven through many of the initial panels.

Posted in Uncategorized | Comments Off
June 3rd, 2009
We’re moving through our third day of presentations and we’re popping up in more news across the web. Check out the link list below and if you’re live blogging or covering the conference let us know in the comments!
Conference notes – CFP 2009, Collin McKay, Office of the Privacy Comissioner of Canada Blog, 6-3-09
The tug-of-war between security and privacy, Max Cacas, Federal News Radio 6-3-09
Tech Policy, Broadband Still at Top of Obama’s List, Says Crawford, Andrew Feinberg, Broadbandcensus.com, 6-2-09
Obama Team Stumps for Tech Policy, Kenneth Corbin, Internetnews.com, 6-2-09
Is There Life After Craigslist for Craig? Maybe, Kenneth Corbin, Internetnews.com, 6-2-09
Securing New Infrastructure Will Require Watchful Eye, Experts Say,Douglas Streeks, 6-2-09
Critics: Google Book Deal a Monopoly, Privacy Debacle, The Future of Less, 6-2-09
Ex-Fed: Privacy Advocates Should Go After China, Lay Off NSA, As in the Days of Noah, 6-2-09
Tags: CFP&N
Posted in Uncategorized | Comments Off
June 3rd, 2009
Another great recap from Wendy M. Grossman at net.wars.
One hundred and thirty-three days into the Obama Administration. He still still has a lot of fans – one conference attendee was wearing silver Obama logo earrings yesterday and CNet writer Declan McCullough was pleased that a FOIA request that kept him waiting for over a year was answered within a few weeks of the inauguration – privacy advocates are beginning to carp that his record on privacy seems unlikely to be any improvement on his immediate predecessor’s. Kicking off the day’s first session, Susan Crawford talked some good principles, but a basic one – answering public questions – was off-limits. `
McCullough also noted that Obama has yet to fulfill his promise to post non-emergency legislation for public comment for five days before signing it.
More>
Posted in Uncategorized | Comments Off